Keyruptive v2.0
A crypto wallet focused on security and convenience.
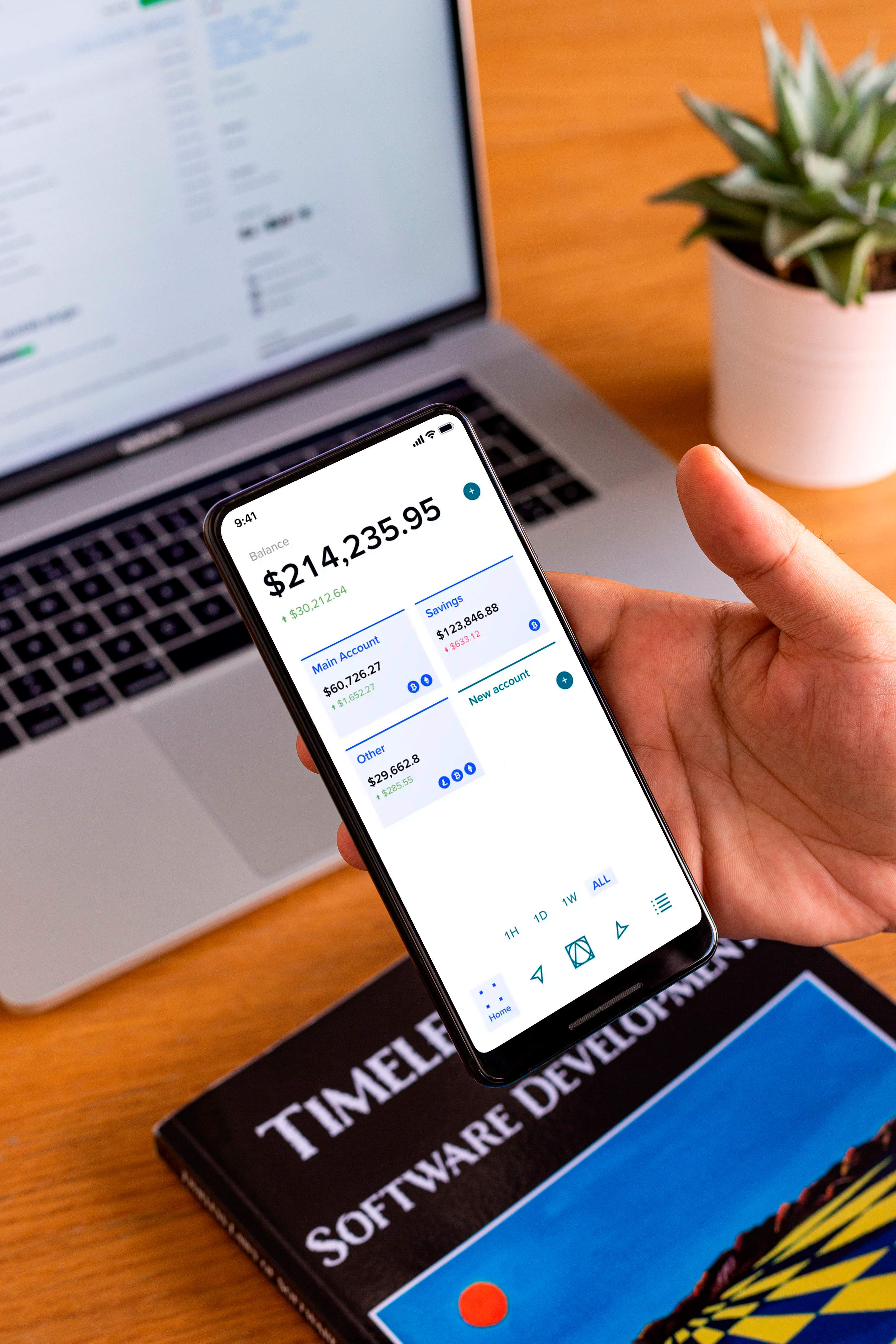
Keyruptive offers a similar security level as hardware wallets through its patented solution while maintaining the convenience of a home banking application.
OUR ROLE Product market fit, research and development
SOLUTION
The Keyruptive solution was designed to be as friendly and convenient as possible. Recognizing the importance of
accessibility and convenience in the world of finance, the team made a strategic investment in a product that
provides users with a mobile-first experience. By prioritizing mobile functionality, the product enables users
to access their funds seamlessly and securely from anywhere at any time.
One of the main goals was to offer the same security level as a hardware wallet in a software wallet. To embrace
that, the solution was thought with the premise that security should be taken for granted by the users. To do
that, the following principles were followed:
No single point of failure
The Keyrouptive algorithm transforms the user keys into multiple chunks and allows users to store them in secure
clouds that only they control. By splitting the keys and storing them across different devices and locations,
it’s possible to guarantee that even if the system is compromised the user funds are safe.
No funds lost
By keeping the keys divided and backed up in multiple locations, the security of the system is leveraged.
However, users can still use the traditional mnemonic mechanisms to recover or import their keys. This
guarantees that a user, in the unlikely event of losing access to a cloud service or the service is down, is
still able to access his funds.
Only users control their keys
Although key data is distributed across multiple cloud providers, the users should be in control of all of them.
Meaning that Keyrouptive doesn’t have any access to the user assets, the user fully owns and controls their
funds. Additionally, the user key is only materialized by the Keyruptive application, in memory, for the time
needed to sign a transaction.
KEYRUPTIVE V2.0 The new iteration of Keyruptive is still an ongoing process. We are currently researching how to leverage it using the same security foundation while enhancing the overall user experience with more modern approaches such as social logins, account abstraction, or multi-party computation. Stay tuned!
TECH STACK
React Native
Visit Keyruptive
